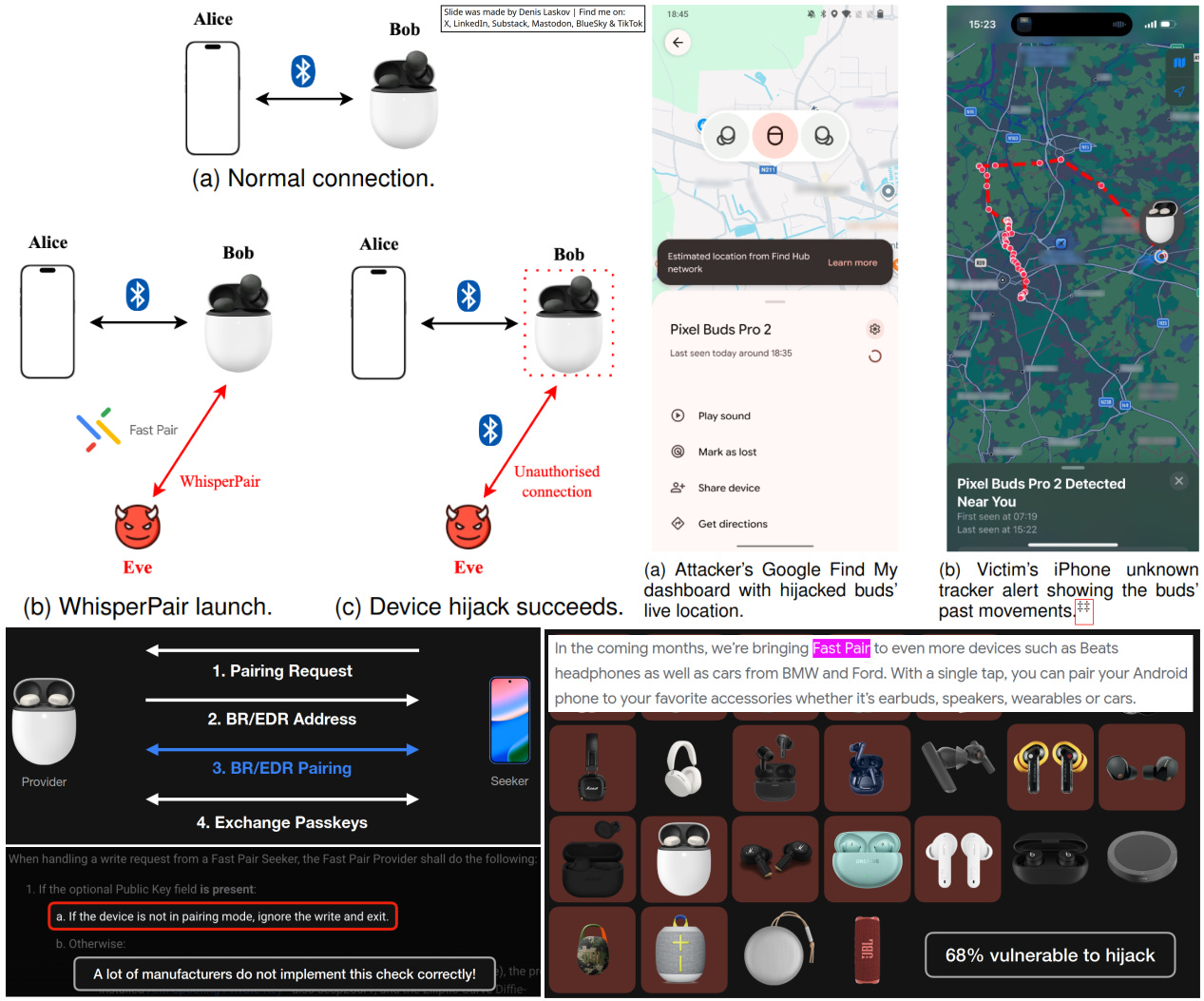
Hacking the Google Fast Pair protocol: Connect to 68% of headphones, earbuds, and cars (?).🎧🚙ᯤ👨🏻💻😱
A group of security researchers (Sayon Duttagupta, Seppe Wyns, Nikola Antonijevic, Dave Singelée, and Bart Preneel) presented earlier this year their extensive research on the Google Fast Pair Protocol and the vulnerabilities they found.
The WhisperPair vulnerability (CVE-2025-36911) is in Google’s Fast Pair system - the Bluetooth technology that makes wireless earbuds and headphones connect instantly with Android devices. The authors show how easy it can be to bypass it.
While the researchers focus on earbuds and headphones, you can find Fast Pair in cars as well. For example, in 2021 Google reported that they planned to include Fast Pair in BMW and Ford cars.
Interesting and highly sophisticated research with a serious impact on the Android ecosystem. Enjoy the read, and please update your devices!
More details:
WhisperPair: A Security Analysis of Google Fast Pair [PDF]: https://i.blackhat.com/Asia-26/Presentations/BHAS26-Wyns-WhisperPair-A-Securi.pdf
One Tap to Hijack Them All: A Security Analysis of the Google Fast Pair Protocol [PDF]: https://whisperpair.eu/whisperpair.pdf
Google FastPair on BMW and Ford [Blog]: https://blog.google/products-and-platforms/platforms/android/better-together/