Hacking Infineon’s TriCore proprietary debug protocol: unlocking state-of-the-art security. 🚗🔳⚡🔓📖
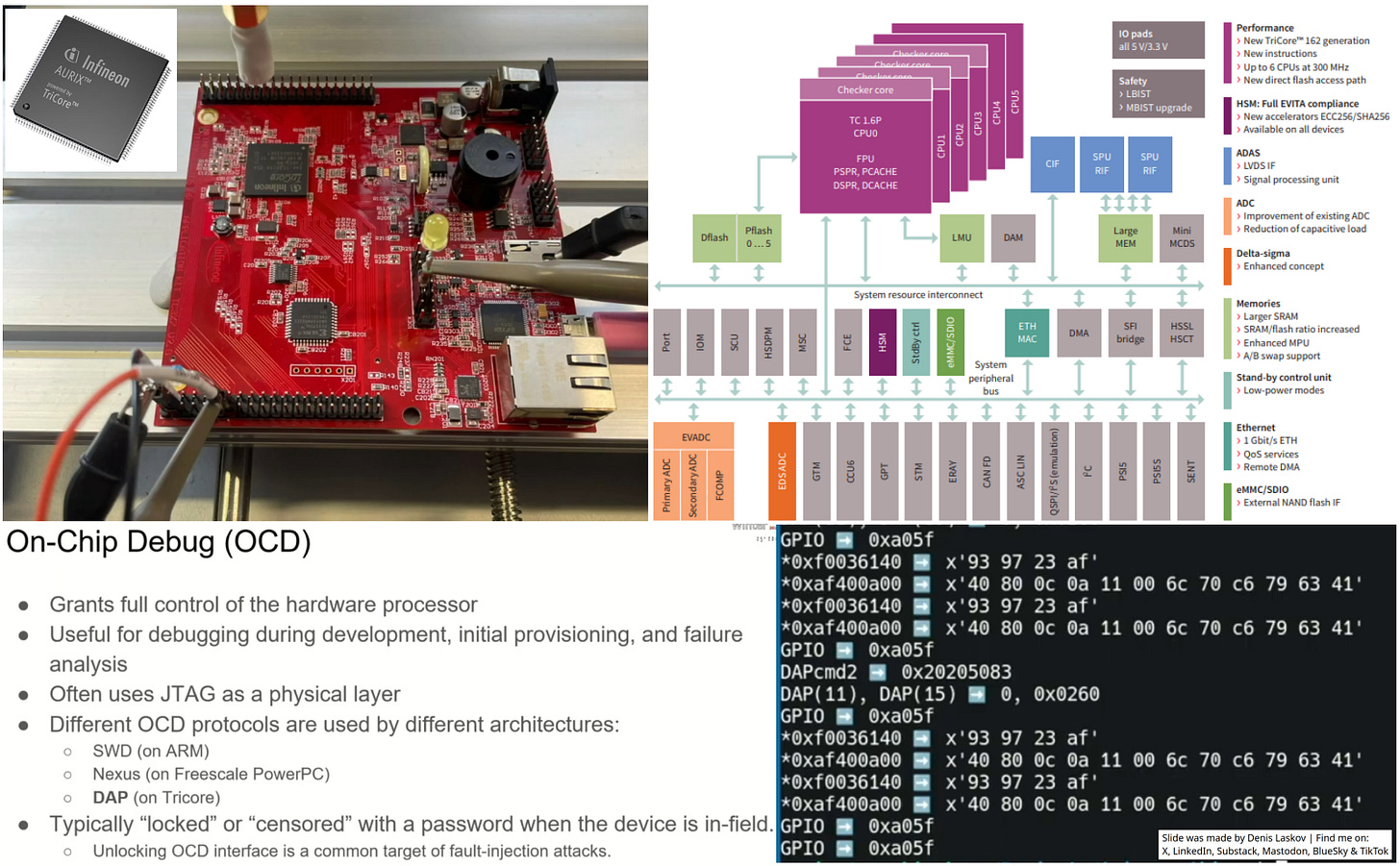
Security researcher Enrico Pozzobon reverse engineered the proprietary DAP on-chip debug protocol used by Infineon’s TriCore automotive microcontrollers - which is quite useful for car hacking.
TriCore microcontrollers are very popular in modern vehicles, especially for ECUs with rich functionality, like gateways, engine controllers, and immobilizers.
The attack code itself is not public [yet], but I believe the talk provides enough information for a security assessment and TARA of your ECU (if you work in automotive cybersecurity), as well as tips on where to dig deeper to follow the author’s steps.
Very interesting research, strongly recommended for anyone interested in hardware hacking and automotive cybersecurity.
More details:
Reverse engineering of the TriCore Aurix debug protocol [Youtube]: https://lnkd.in/eXiCCF_8
Code [Github]: https://github.com/epozzobon/tricore-things