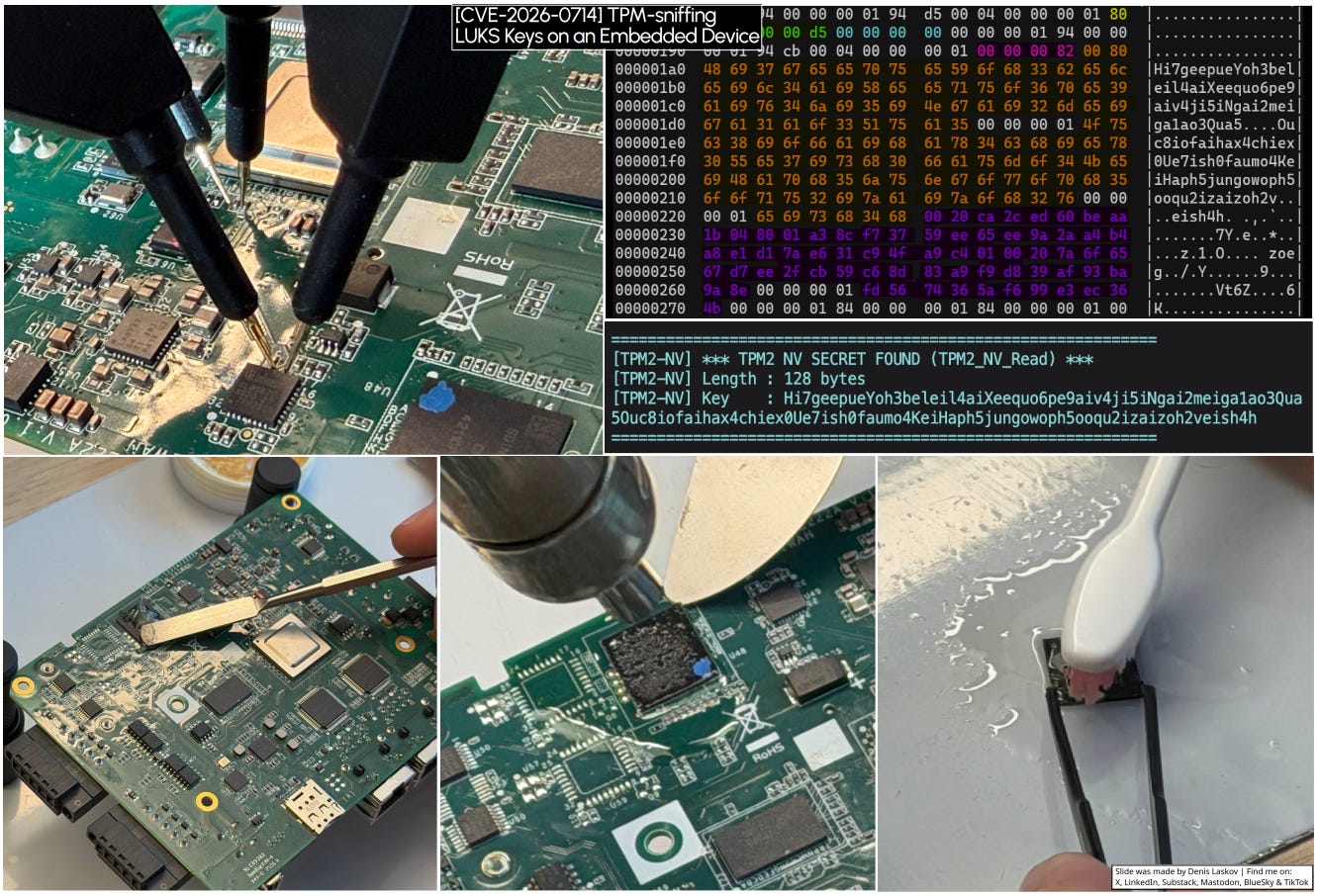
Hacking a Linux device with TPM + LUKS encryption: extracting the TPM key from SPI in plaintext. 🐧💻👂🔑🎉
Security researchers Per Idenfeldt Okuyama and Sam Eizad share technical details of a security vulnerability (CVE-2026-0714) discovered in the Moxa UC-1222A Linux device that uses a discrete TPM 2.0 chip to protect LUKS encryption keys.
With physical access, an attacker can tap into the SPI pins on the board and sniff the encryption key in plaintext from the SPI interface using a relatively inexpensive logic analyzer. As simple as that.
Now, this is a vulnerability in one specific device, but the approach is quite promising.
AFAIR, this is the first public attack of this kind on Linux systems, and not on Windows/BitLocker. Enjoy the read, and please share it with your colleagues and people who should know about it. :)
More details:
[CVE-2026-0714] TPM-sniffing LUKS Keys on an Embedded Device [Blog]: https://www.cyloq.se/en/research/cve-2026-0714-tpm-sniffing-luks-keys-on-an-embedded-device