Breaking into secure wireless networks: Wi-Fi client isolation is broken, and here’s how. 🛜💉👨🏻💻🏴☠🌎
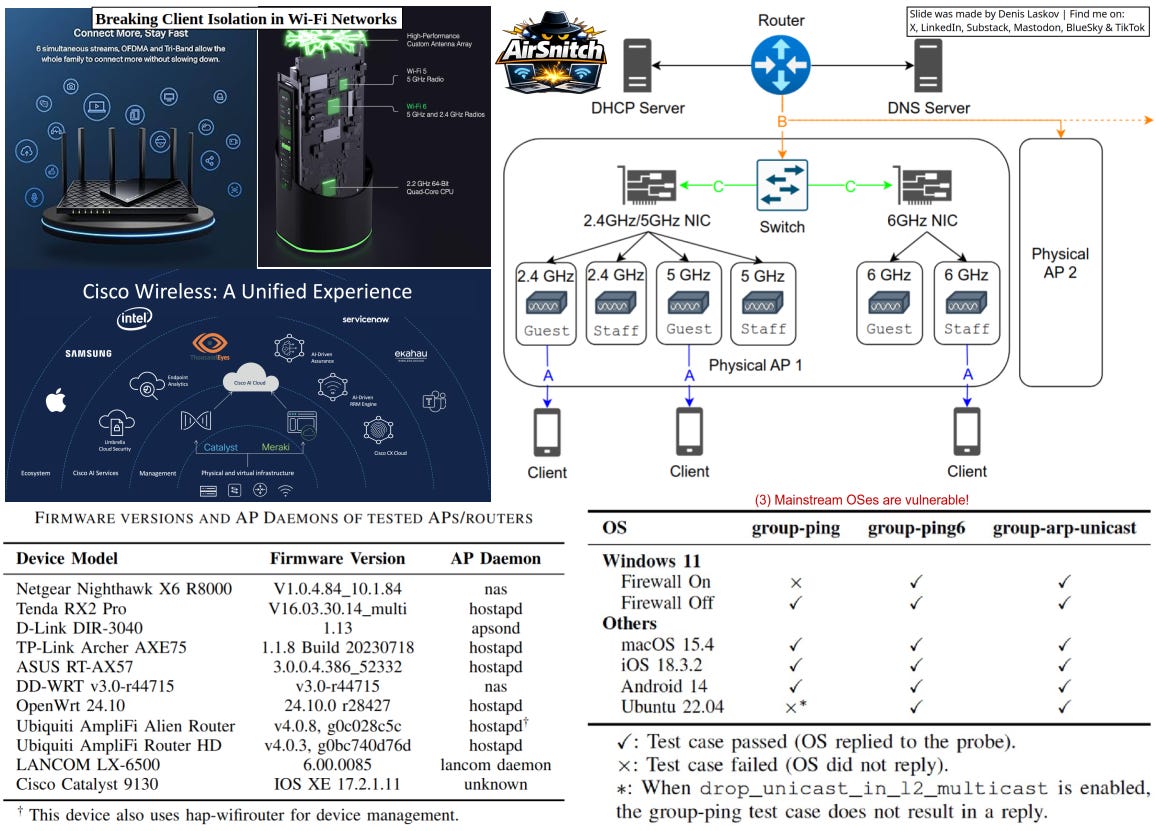
An international group of security researchers published research in February 2026 on the client isolation feature in Wi-Fi networks, and their conclusion is that this feature is broken and unreliable.
In simple words: an attacker with access to one (guest?) network can spy on others’ (internal or “secure”) Wi-Fi traffic without breaking encryption. Guests in offices, passengers on airplanes?
All types of Wi-Fi network encryption are affected - from WEP to WPA3 Enterprise - because the problem is not in the encryption, but in how networks handle traffic.
What can be done so far:
Inject fake data into a victim’s traffic
Intercept (spy on) traffic
Become a man-in-the-middle (MitM)
Corporate IT, smart cities, healthcare, automotive, aviation, and industrial security people - please check the details and see how your field is affected. I believe it is.
It looks like we can officially remove client isolation from the list of security features for Wi-Fi networks? Great find and serious impact! Enjoy the read.
More details:
AirSnitch: Demystifying and Breaking Client Isolation in Wi-Fi Networks
Paper [PDF]: https://www.ndss-symposium.org/wp-content/uploads/2026-f1282-paper.pdf
Presentation [PDF]: https://www.ndss-symposium.org/wp-content/uploads/f1282-zhou-slides.pdf
AirSnitch [Github]: https://github.com/zhouxinan/airsnitch